IPHONE APPS WITH FAKE LOGIN POP-UPS CAN STEAL YOUR PASSWORDS
Malicious iPhone apps can steal users’s personal information through fake login pop-ups,…
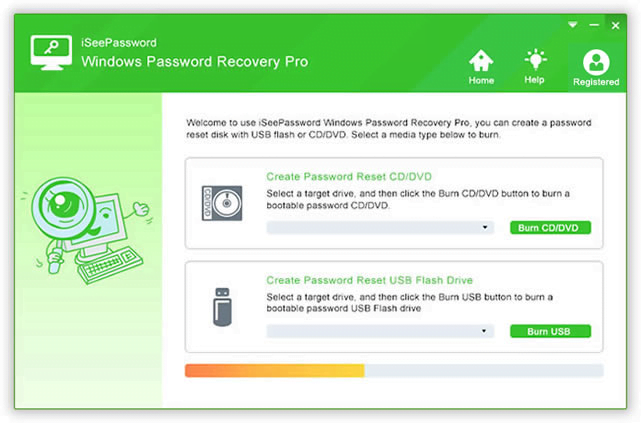
Locked out of Windows 10, How to Reset Windows 10 Login Password?
Windows 10 which was launched by Microsoft and keeps updating. It offers…